lopes.log
where others see logs, I see stories.
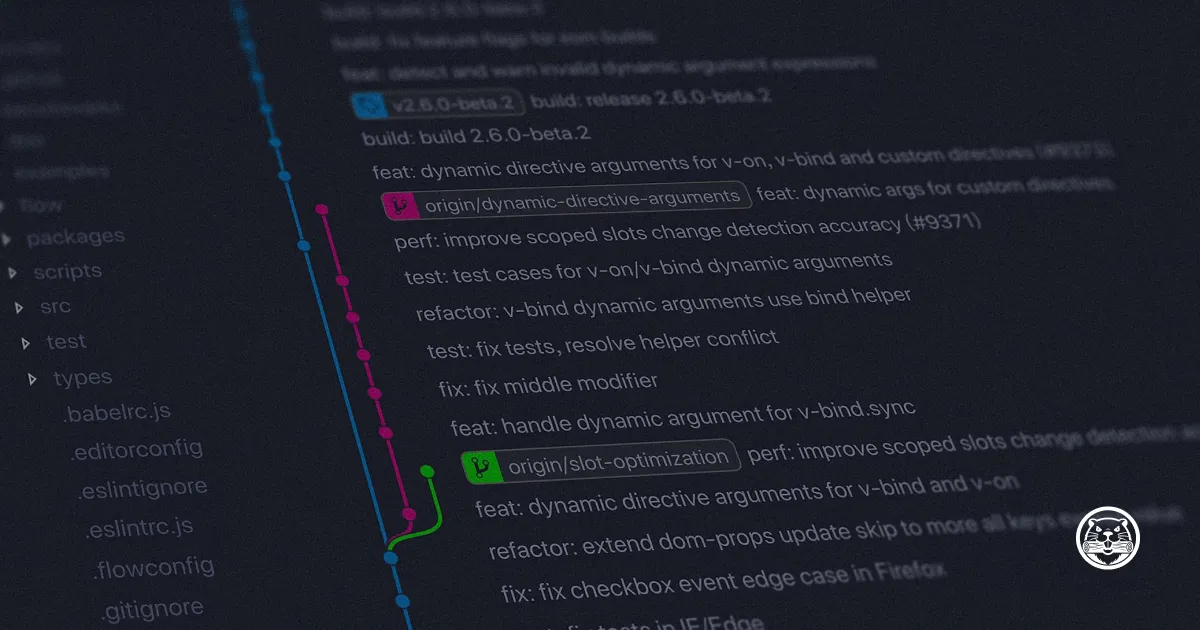
Auto-Cleaning Data Tables in Chronicle SIEM
logging
cloud
dev
detection
Review: A Bug Hunter’s Diary
career
intel
hardening
unix
Auto-Cleaning Lists in Chronicle SIEM
logging
cloud
dev
detection
Review: The Cuckoo’s Egg
dfir
detection
intel
Insights into Effective SIEM Deployment
logging
detection
dfir
No matching items